How can spyware be identified?
Don't Get Fooled By SPYWARE

Hasan Mahmud is the Managing Director of Cyber Aeronautycs Ltd. and CTO of SECROOQ LTD.
He helps producing actionable intelligence to protect against cyber threats by working behind the scenes to identify network and application-based vulnerabilities to businesses.
Hasan has 12 years of experience where he applied his expertise and knowledge of threat actors’ tactics, techniques, and procedures to help develop signatures and mitigate attacks proactively for customers.
Spyware may be a user's worst enemy. When spyware infects a user's device, it can gather a range of personal and sensitive information, depending on the type of malware. Here's all you need to know about spyware and how to spot it.
What exactly is spyware?
Spyware is a sort of malware that infects a user's computer and continually monitors the system, including keyboard activity, the user's online surfing patterns, screenshots, and email activity. Spyware can also activate the user's webcam and monitor their activities in real time.
If spyware is not removed, it might infect the user's computer with other forms of malware or otherwise harm the machine. It will also communicate the sensitive information it obtains to another business, who will utilize the information to damage the user, such as selling it to a third party or stealing their identity.
There are several sorts of spyware.
There are several varieties of spyware that can employ similar strategies to target a user's computer or network and are not mutually exclusive. Here are the most dangerous forms of spyware.
Monitoring the System:
Because it records a user's computer actions - keystrokes, visited websites, search history, email activity, chat and messaging conversations, and system credentials such as logins and passwords - this sort of malware is also known as keylogger.
Trojan:
There are many different varieties of Trojans, and spyware is one of them. A trojan is a sort of standalone malware named after the ancient Greek fable of the Trojan Horse. It may appear to provide some helpful feature while dumping a dangerous payload in the background. These payloads can transfer ransomware and other malware onto the computer, delete files, provide unwanted access to personal information, steal credentials, change online transactions, and so on. When users enter into financial or banking websites, banking trojans steal their credentials.
Browser password and Infostealers:
This sort of spyware collects passwords and valuable information from any source that the user uses to obtain passwords, login credentials, and other sensitive data.
How does a user get spyware?
Spyware may infiltrate a user's PC in the same manner that other forms of malware can. When a user mistakenly clicks on an infected email link (phishing), visits a malicious website, or downloads software from an untrustworthy site, it can exploit browser security weaknesses to show an infected ad or infect a device. In addition, you might become infected by clicking on strange social media or SMS communications.
How can spyware be identified?
Many times, spyware will create unexpected computer difficulties, such as:
- Spinning apps during startup and shutdown, as well as delayed system response
- Increased frequency of banner advertisements and pop-ups
- The PC battery is depleting faster than usual.
- Login issues on secure websites
- New programs and utilities not installed by the user
There are several ways to detect spyware:
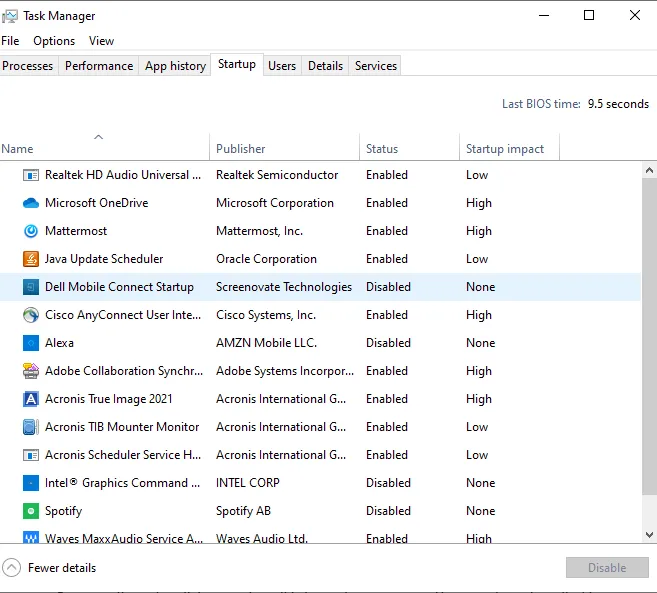
Task Manager's Startup tab Check the Startup tab in Task Manager for suspicious apps on Windows PCs. If anything appears strange, the user should momentarily stop the process and investigate what the application is. If it is malignant, the user should delete it immediately.
Click "Finder" on a Mac and then pick "Applications" from the sidebar. Examine the list of programs once again, and if anything appears strange, do your study and uninstall the app if it is dangerous.
Temporary files The user can also examine their TEMP folder for malware. In fact, because they are temporary files, you may remove everything in the temp folder simply to be safe.
Install anti-virus software.
Installing an anti-malware solution and scanning the computer is the best technique to identify and remove spyware. Reputable suppliers' solutions will detect and remove spyware from the PC.
Is it possible to install spyware on your mobile phone?
Yes. Spyware may infect both iPhones and Android phones. On a mobile device, spyware operates undetectedly, monitoring and recording the actions of the user without their knowledge. It can monitor call records, contact lists, images taken on a user's phone, a user's location, and even record and photograph everything heard through a device's microphone.
CAL Defense from Cyber Aeronautycs Ltd. identifies and eliminates spyware.
Cyber Aeronautycs Ltd. provides complete cyber security solutions that identify and eliminate malware. If you are a business seeking for the best antivirus software, CAL Defense secures the devices of your remote workers in the post-pandemic world. The solution offers a one-of-a-kind combination of data protection and next-generation cybersecurity capabilities, resulting in greater security and cheaper costs.
CAL Defense, whether large or small, automates and simplifies system and data security to limit risk and avoid downtime.
If you are a managed service provider (MSP), Cyber Aeronautycs Ltd. Safeguard Cloud, a solution that enables you to supply cyber security in a simple, efficient, and secure manner, can protect your clients' computers. Your clients can achieve the maximum in data safety with hybrid cloud backup, disaster recovery, and ransomware and spyware protection all from a single platform. Endpoints, including remote devices, systems, and data are all protected by CAL Defense Cloud. It also offers AI-based behavioral detection to prevent zero-day attacks, URL filtering and vulnerability assessments, video conference protection, and automatic patch management.
With the power of CAL Defense, you can identify and halt cyberattacks of any kind, ensuring that your clients' data and systems are recovered as quickly as possible.





